How to Hack WPA2 Wi-Fi Passwords Using Jedi Mind Tricks (& USB Dead Drops) « Null Byte :: WonderHowTo

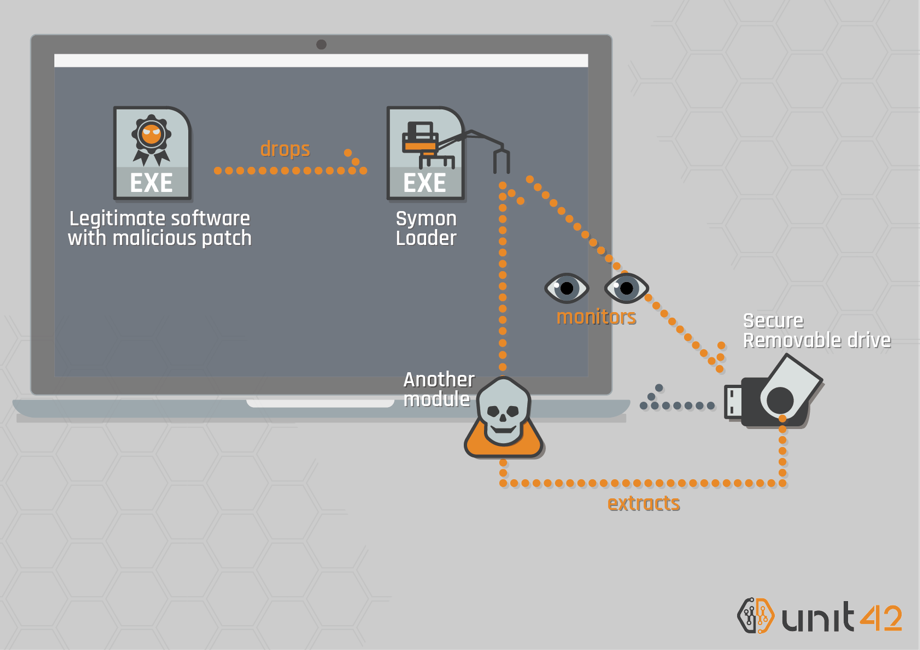
Cybrary - 💻FREE COURSE 📚 "USB Drop Attack" - Discover how attackers disguise attacks to make them successful https://app.cybrary.it/browse/course/usb-drop-attack | Facebook