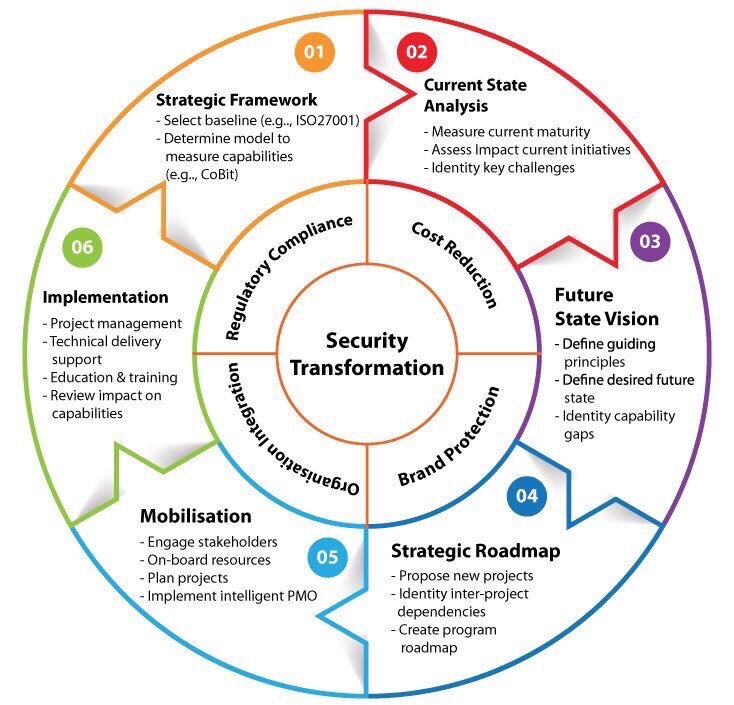
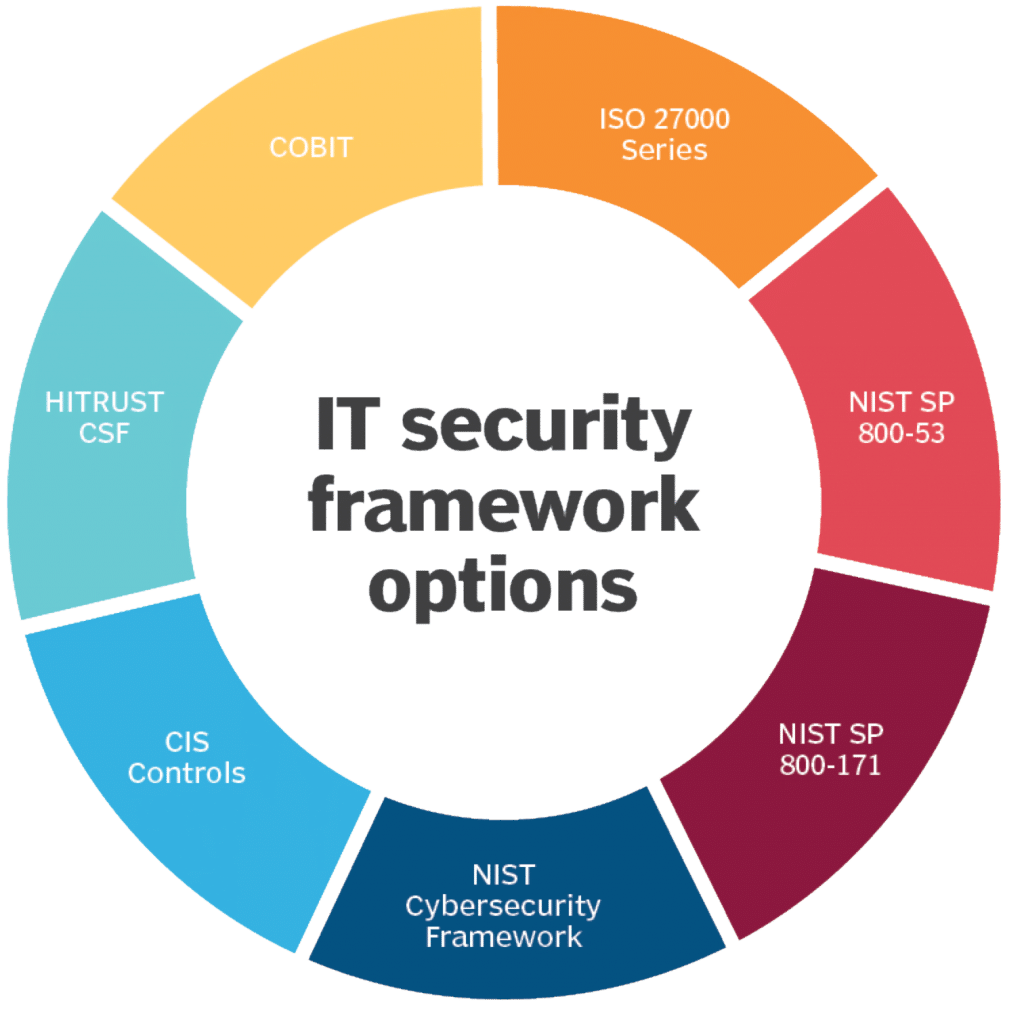
Information Security Program Assessment | Information Security Governance | GRC Solution | Corporater

Security & Privacy By Design (SPBD) - Comprehensive cybersecurity for privacy by design program template and checklists
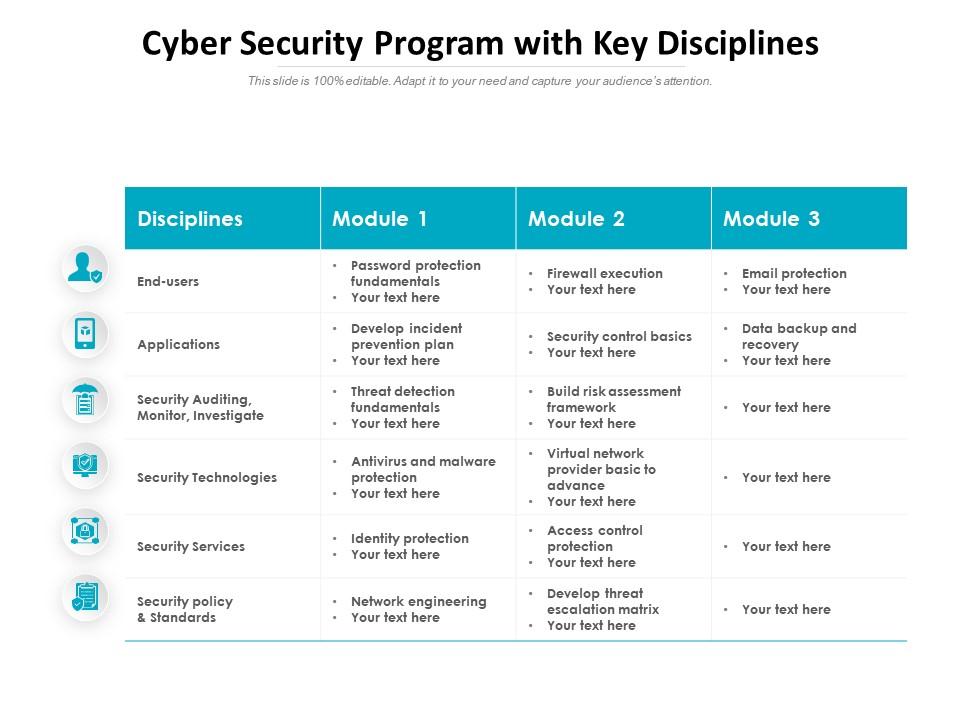
Cyber Security Program With Key Disciplines | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

CICRA Consultancies - CICRA HUB online Cyber Security Awareness Training is a continuing educational program that empowers employees with knowledge and skills to face potential Cyber threats; the program covers all aspects


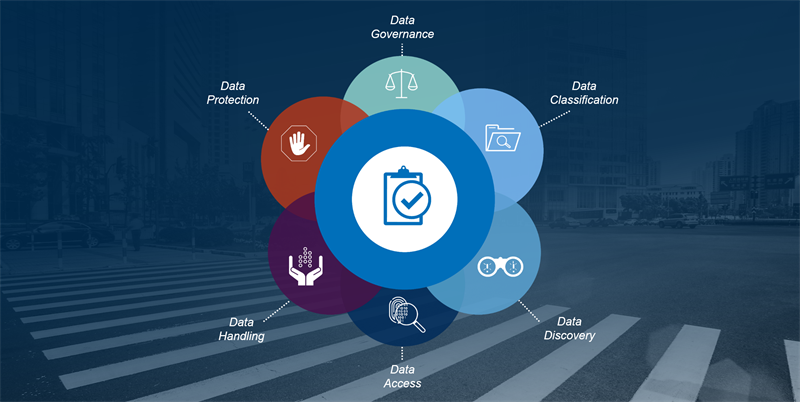






![Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager](https://dataprivacymanager.net/wp-content/uploads/2020/08/visual-representation-of-data-privacy-and-data-security-areas.png)



![Withdrawn] 10 Steps: Summary - GOV.UK Withdrawn] 10 Steps: Summary - GOV.UK](https://assets.publishing.service.gov.uk/government/uploads/system/uploads/image_data/file/35242/10_steps_to_cyber.png)